Why software protection matters
- Most PC games suffer from piracy
- The first weeks after a games initial release are most crucial, as the majority of sales are made in that timeframe
- Comparisons between protected and unprotected sequels of games show around 30% of loss in revenue for publishers not applying effective anti-piracy measures
What sets our product apart
Designed from the ground up by security experts to fit the specific needs of the highly exposed PC gaming industry.
Easy Integration
Integrating our protection into your game does not require expert knowledge or time-consuming effort from your engineers.
Extensive Compatibility
The protection does not require installation of custom drivers and is tested rigorously across hardware configurations to ensure maximum compatibility.
High Performance
There is no noticeable impact on gaming performance or user experience in case of protecting your game with our technology.
No Permanent Connectivity
Our protection system does not require always-on internet connectivity.
Strong Security
Our highly secure protection technology is improved continuously, providing significant crack-free timeframes.
Development Friendly
Protected executables do not harm engineers ability to perform crash dump analysis.
How our security works
aderow´s security architecture is designed by industry experts to protect PC-based video games against piracy during their critical initial sales window.
We achieve this by countering reverse engineering attacks with the latest technologies. The following section describes some of the security features in detail.
Code Obfuscation
Code obfuscation conceals the purpose of machine code, therefore making it harder to read and reverse engineer.
Virtual Machine
Our virtual machine technology provides state-of-the-art code obfuscation capabilities. It translates security-relevant code portions into a tailored instruction set that is interpreted by a virtual machine at run-time. This results in an increase of code complexity by an order of magnitude making reverse engineering exceedingly difficult.

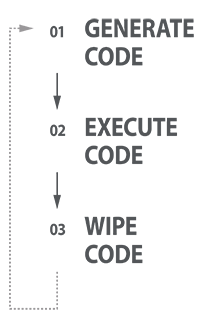
Just-In-Time Code generation
Just-In-Time compilation is a method of translating code at run-time rather than at compile-time. aderow´s security products utilize this technology to effectively counter attacks that aim at modifying machine code.
Protection Workflows
How to integrate our protection
- The game is profiled by aderow prior to the gold master date
- The game studio integrates the protection client into the build environment
- The game executable is transmitted to our cloud-based protection system
- Our protection system automatically protects functions that are not executed during game-play and provides the protected executable

How protected games are activated
- On first-time use a connection to our activation system is established
- The end-user provides a hardware fingerprint identifying his computer system
- A license is transferred to the end-user and stored locally for offline use

